Shor’s algorithm, when run on a sufficiently massive quantum pc, could effectively factorize integers and clear up the Discrete Logarithm Drawback, breaking RSA, Diffie-Hellman, and ECC. The basic operation in ECC is the addition of points on an elliptic curve. Interestingly, this operation doesn’t correspond to standard addition but entails drawing a line via two points and determining the place it intersects the curve a third https://eherbcenter.com/buying-and-selling-system-software-program/ time.
- Right Now, most information remain protected with present requirements, however systems (and HSMs) are being upgraded to support NIST’s post-quantum algorithms in preparation for the arrival of large quantum machines.
- Use your instruments to apply different keys, algorithms, or strategies to the problem.
- Cryptocurrencies like Bitcoin and Ethereum are constructed on advanced data encryptions that require significant quantities of computational power to decrypt.
- Be Taught about cryptography, its important position in cybersecurity, various sorts, algorithms, risks, and future trends.
Advanced cryptographic algorithms use these bits to rearrange and scramble the plain textual content information into ciphertext. As the variety of bits increases, the variety of total attainable preparations of the info rises exponentially. Cryptology, which encompasses each cryptography and cryptanalysis, is deeply rooted in computer science and superior mathematics. The historical past of cryptography dates again to ancient instances when Julius Caesar created the Caesar cipher to obscure the content of his messages from the messengers who carried them within the first century B.C.. At Present, organizations just like the Nationwide Institute of Requirements and Know-how (NIST) continue to develop cryptographic requirements for information security. Alice uses that key to encrypt the message, and Bob makes use of the identical one to decrypt it.
Still, the move to OpEx makes encryption tools accessible to smaller teams and aligns prices with actual wants. Companies that when wanted huge budgets to justify HSMs can now start small and develop their encryption footprint organically. Many teams find that help contracts and staff costs exceed the initial hardware spend over several years. Addressing these deployment challenges head-on is significant, as they represent some of the most persistent encryption challenges enterprises face right now. If not using the OTP, anybody who’s even remotely thinking about figuring out what you wrote and knows about cryptography will be ready to break the encryption. In The Meantime, Ilango was impressed to attack the problem after discussions with other researchers, together with Santhanam, on a visit to the Simons Institute for the Concept of Computing in Berkeley, California.
Knowledge Integrity
Such side-channel assaults let the bodily implementation of the cryptosystem be the goal somewhat than the algorithm itself. Usually in cryptography, timing data, power consumption, and electromagnetic emissions are completely neglected relating to the implementation of the cryptographic primitives in apply. This complete information supplies a deep dive into cryptographic challenges, equipping professionals with the knowledge and tools needed to secure data effectively. These applications spotlight the critical role of cryptography in mitigating cybersecurity threats.
It’s about trusting that your messages are secure, your information is undamaged, and the particular person on the opposite end is actually who they are saying they are. Even if an adversary is conscious of the encryption methodology, the message cannot be decrypted with out knowing the important thing (shift value). Sometimes, cryptography can secure and verify cryptocurrency transactions for blockchain-based currency like Bitcoin.

Superior Technologies Of Quantum Key Distribution
Even with three layers of encryption protecting your information, there might be still the problem of transferring the key to your app securely. Ideally this involves authentication between your app and the key management server in addition to supply explain cryptography over an encrypted connection…a fourth layer of encryption. There are also efficiency considerations such as securely caching the key in memory which can be difficult. Cryptography is also used for frequent messaging applications like e mail and WhatsApp to provide end-to-end encryption (E2EE) and maintain the privateness of users’ conversations. With E2EE, only the sender and supposed recipient can decrypt and read their messages, making it almost unimaginable for third parties—including users’ personal service providers—to access the content.
Modern Cryptography Considerations
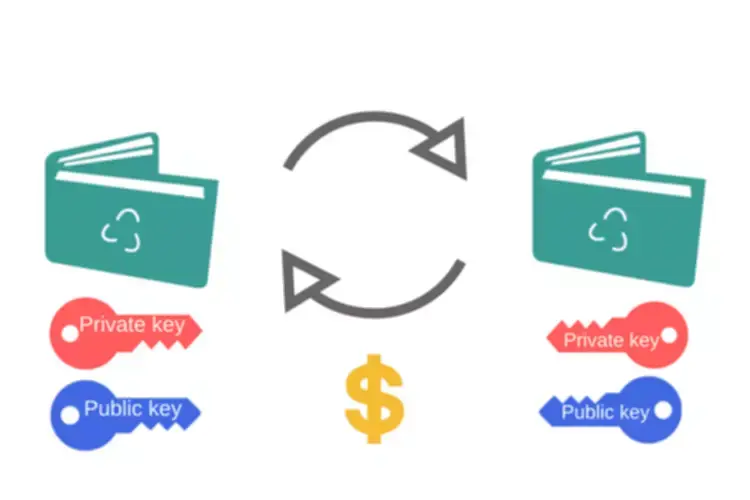
Nonetheless, it’s not with out its complexities and vulnerabilities. In ECDH, two events Constant function market maker individually choose non-public keys and compute their corresponding public keys by performing scalar multiplication on a predefined generator level G of the elliptic curve. The public keys are exchanged, and each celebration computes the shared secret by multiplying their non-public key with the obtained public key. The ElGamal encryption system can be adapted to work with elliptic curves. Related to ECDH, the events first agree on an elliptic curve and a degree on the curve. The sender then chooses a random number as the private key and computes a public key.
Fiber optic strains are needed for transferring photons and have a restricted vary of usually about 248 to 310 miles, which pc science researchers are working to increase. Additionally, quantum cryptography systems are restricted by the number of locations the place they can ship information. Since most of these techniques depend on the precise orientation of unique photons, they’re incapable of sending a sign to a couple of intended recipient at any time. We stay in a world where nearly every little thing, like shopping, banking, chatting, and even unlocking your front door, happens online. With Out cryptography, all of that information can be uncovered, like sending a postcard as an alternative of a sealed envelope. Cryptography retains delicate data (like passwords, bank card numbers, and private messages) hidden from hackers, scammers, and eavesdroppers.
Make sure that you simply only use algorithms, key strengths, and modes of operation that conform to trade best https://www.xcritical.in/ practices. Advanced encryption normal (AES) (with 128, 192, or 256-bit keys) is the usual for symmetric encryption. RSA and elliptical curve cryptography (ECC) with no less than 2048-bit keys are the standard for asymmetric encryption. Be positive to avoid insecure modes of operation corresponding to AES in Digital Codebook (ECB) mode or RSA with no padding.
ECC is utilized in several cryptographic protocols, including variants of Diffie-Hellman and ElGamal, which we are going to discuss intimately. The class P, or ‘Polynomial time’, includes problems that may be solved shortly (in polynomial time) by a deterministic Turing machine, an abstract computational model. External audits or penetration checks typically embrace attempts to misuse keys or bypass encryption, guaranteeing the system’s controls work. In a zero-trust structure, all information, whether in transit or at relaxation, is often encrypted.
